We spent this morning with the students involved in the Drexel University Computing Academy, which I’ll now refer to as “DUCA.” I provided a link in the first sentence, and this looks like a great programs for students. From the website:
DUCA is a five-week, residential, summer computing program at Drexel University in Philadelphia, PA that promotes interest in information technology, computer science, business and digital arts & media. DUCA students do not focus on one specific area of computing. Rather, the program has a more holistic approach to education, exposing students to a variety of fields in computing through interactive, group projects.
What Students Explore:
- Information Technology
- Game Design I Game Development
- Robotics
- Computer Networking I Security
- Social Media I Web Development
What Students Gain:
- An authentic college experience
- Critical thinking skills
- Leadership skills
- Friendship
- Confidence
The program is open to current high school sophomores and juniors. Students within the United States and international students can apply.
The Drexel University Computing Academy Scholarship is available to incoming freshmen students who have participated in the summer academy program. Recipients will receive $1,000 for each quarter they are enrolled full-time in classes and provided they maintain a minimum 2.75 cumulative GPA. This award will not be applied in excess of 12 academic quarters and pays towards tuition only.
The Eugene and Meher Garfield DUCA Scholars Endowed Fund, established in June of 2013, provides funding for a full scholarship for one economically underserved high school student per year from Philadelphia, The Delaware Valley, or Southern New Jersey to attend DUCA. Selection of the recipient shall be determined by the Director of DUCA.
Bill posed this question to the group to preface today’s lesson: “How do we obtain a website, and how does it know how to get to us?” It seems like such a simple question, but the technology and protocols behind this concept are complex. It was interesting to listen to the students theories of how it could potentially work.
One of the next activities we completed was simple: Each group received 5 slips of paper. There is a person (Bill) who acted as a router. You had to get the message (one word per slip to make a sentence) to another group. That group would have to be able to successfully read the message. Most of the groups realized that the “packets” had to be numbered, but not many understood that the packets had to be marked to which group of packets they belonged.
Bill then briefly explained Wireshark, and how you can view your own packets, as well as other’s packets. (He left the malicious uses of Wireshark to the imagination…)
We also talked about how random number generators worked. Something I did not realize: The Nintendo random number generator (RNG) is based on the 1/60th of a second that you hit the “start” button. (60hz=60 frames per second). You can actually game the system, and hit it at a more optimal time to make you faster/have more strength.
We then moved on to a bit of cryptography. We talked about ciphers as they relate to SSL of the tcp/ip protocol. Bill mentioned Adi Shamir- the S in the RSA. He said he’d talk more about that later.
On the cryptography front, we looked at an Undirected Graph, with different nodes (vertices), and connected by line segments. We had to pick a number (which we picked 398 as ours), and put the number in unequal quantities into 10 spots. We then added the numbers attached to each node to make a new total. Bill was trying to guess our number without seeing our number. There are 3 nodes you can add together to get our original number, which was a really cool trick. Pictures:
Original Numbers (crossed out)
Picture 2- added notes together
This led to a discussion about the Public Key vs. Private Key, and how everyone has the public key, but only the website has the private key.
We also did a card trick. The card trick is a random matrix of flipped or not flipped cards. It’s essentially an exercise in binary. We set up a 4×4 matrix. The person who would be trying to guess the card comes over, and adds a column or row. They use this column or row to make it even. If there is one card flipped (1), they add a new card heads up (1), for a total of 2 (now even.) If there is an even number of cards in the row, the card is added face down. It’s a bit hard to explain in words, so here’s an image:
(This is with the row added, but before we flipped a card)
The card exercise prompted a discussion about parity, and ECC. One example is when a CD skips, it can use the information around it (oversampling) to fill the audio bits on the fly.
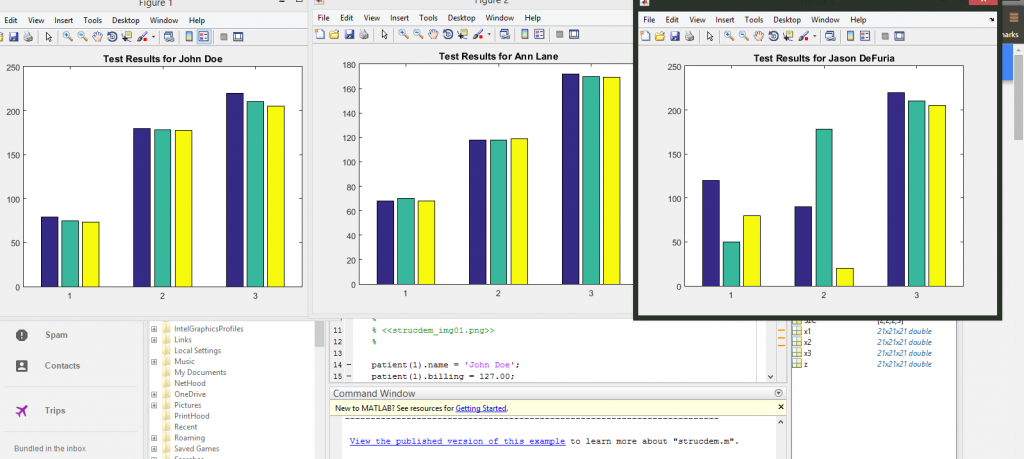
I spent the afternoon today working on more MATLAB tutorials. I also found out about Octave, which is “essentially” a GNU MATLAB.